Protecting your OpenSSH Server
SSH is the most valuable tool to manage your servers. As you already know, SSH allows you to remotely connect to your server and access a shell. With the power SSH possess, it’s important to protect SSH to ensure the only trusted people are able to connect. This post will go through the SSH configuration settings that need to be modified to help protect your server.
Editing SSHD Configuration Files
To prevent this tutorial from repeating itself too frequently, here is an overview of how to edit the /etc/ssh/sshd_config file. OpenSSH’s server configuration file is located at /etc/ssh/sshd_config, which is different from the client configuration file /etc/ssh/ssh_config. It’s possible that SSHD is using a different configuration file if the command line argument -f is being used.
Google Drive Create Envelope Template
Creating an envelope is most office suites only requires you to dive one or two levels into a menu. As for Google Drive, this just isn’t the case. It’s possible to change a Google Drive document’s page setup by navigating to “File - Page Setup”, but there are only eleven predefined paper formats you can choose from. To change the actual dimensions of the Google Drive document, you need to use a Google Apps Script that changes the documents dimensions. If you don’t want to build a script (and I don’t blame you), below is a list of documents with the most common envelope dimensions.
How to Separately Handle Multiple Website Deployments
Uploading website files routinely can become a chore, and no one wants that. Queue a deployment script, at the very least, it’s a script that uploads files to the server, but can be as advanced as verifying files once uploaded, run code tests, and update database structures along. There are two different methods to run a deployment script. First being automated deployment with continuous integration systems to a staging or production servers. The second method is to manually run the deployment script when you’re ready to upload changes onto the servers. It’s not uncommon to see both methods used, with automated deployment to a staging server and manual deployment to the production server.
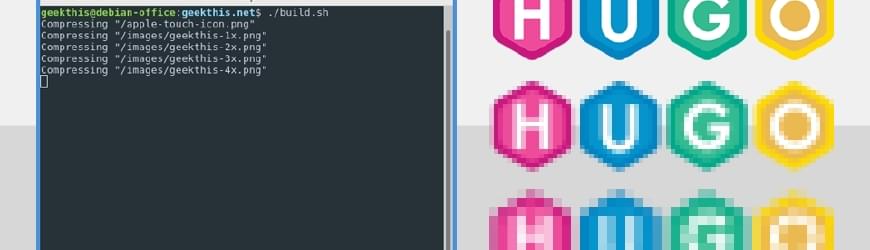
Build Script for Hugo Websites
Over the past year I’ve been building many websites using Hugo. Early on in development of these sites, I noticed the need for a build script. My main goal of the build script was to store the original uncompressed images inside my website’s code repository and have the built version of the Hugo website use compressed images. In addition to compressing images, I also needed a method to compress style sheets and JavaScript files. Below is an outline of how my build script works, code snippets that may be useful if you’re creating your own build script, and at the end of the page the full version of my build script.

Nginx Logging Privacy and Security
Below you will learn how to configure Nginx to stop logging sensitive information and help protect the privacy of your users along with protect authorization keys and query strings from being logged. Each section below outlines how to stop logging a specific page or piece of information. Multiple sections below can be combined to fully customize how you log visitors to your website.
Basics to Nginx Log Options
Before actually modifying any configuration files, here is an overview of the Nginx log options we will be using. Quickly, Nginx configuration files are generally stored in the directory /etc/nginx/, with site specific configuration options beings stored in separate files inside the directory /etc/nginx/sites-available/. The main Nginx configuration file is /etc/nginx/nginx.conf.